Question:
After the 30th of May 2020, my website certificate becomes untrusted. Why and how to fix that?
Answer:
On May 30, 2020, 10:48:38 +0000 root certificate "AddTrust External CA Root" and intermediate certificate "USERTrust RSA Certification Authority" expired.
That could impact leaf certificates validation on outdated systems.
Modern browsers are not affected by the expiration since they automatically switch to the new SHA-2 root (Comodo or USERTrust).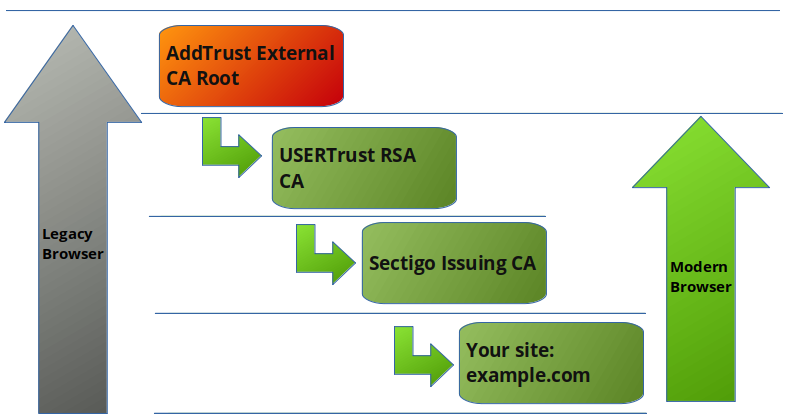
If your service meets one of the following conditions, it may be affected:
- Your application is set up to explicitly trust Addtrust External CA Root ;
- Your service is using the expired Root certificate and is being accessed by applications other than browsers (e.g. API, cURL, OpenSSL, etc.) ;
- Your service is using an application that has not received security updates since mid-2015 ;
- Your service is using an application with broken certificate path validation (e.g. OpenSSL, OpenLDAP, Postfix) ;
If your service uses one of the affected applications regardless of the Root certificate installed, you should update the settings of the affected application.
Follow this guide to check if your service is using the expired Root:
- Start OpenSSL
openssl s_client -connect remote.host:443where "remote.host" equals your domain name ; - If you see AddTrust External CA Root as CN, please follow the next steps.
Otherwise, the service is not affected by the issue.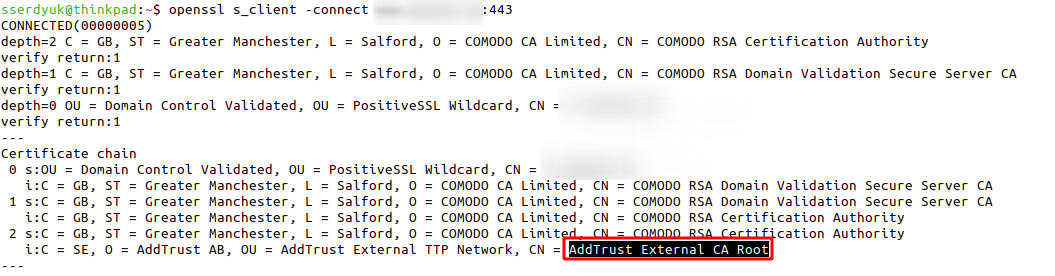
To fix any issue reinstall root and intermediate certificates bundle.
Check your "Issuer Common Name" using OpenSSL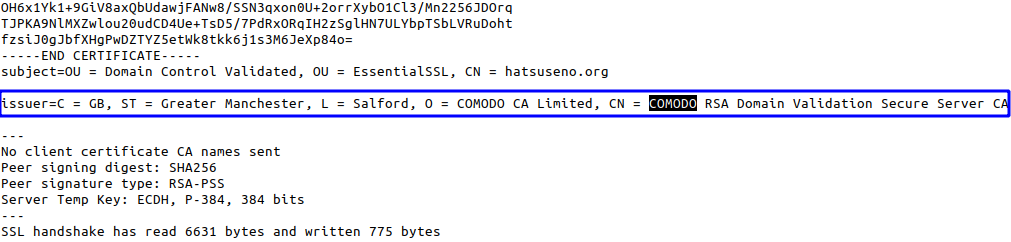
Depending on your current vendor use following root and intermediates (updated 03.06.2020):
| Product | Domain Validation | Organization Validation | Extended Validation |
| Comodo | root | int | root | int | root | int |
| Sectigo | root | int | root | int | root | int |
| Sectigo with AAA root (for legacy devices) |
root | int | root | int | root | int |
