Answer
OCSP - Online Certificate Status Protocol.
Purpose: verify the validity of the SSL certificate to be sure it's not revoked.
The encryption itself is meaningless unless additional measures are implemented, among which you can check the status of the SSL certificate. The certificate must not be revoked or expired if another - it will not be trusted.
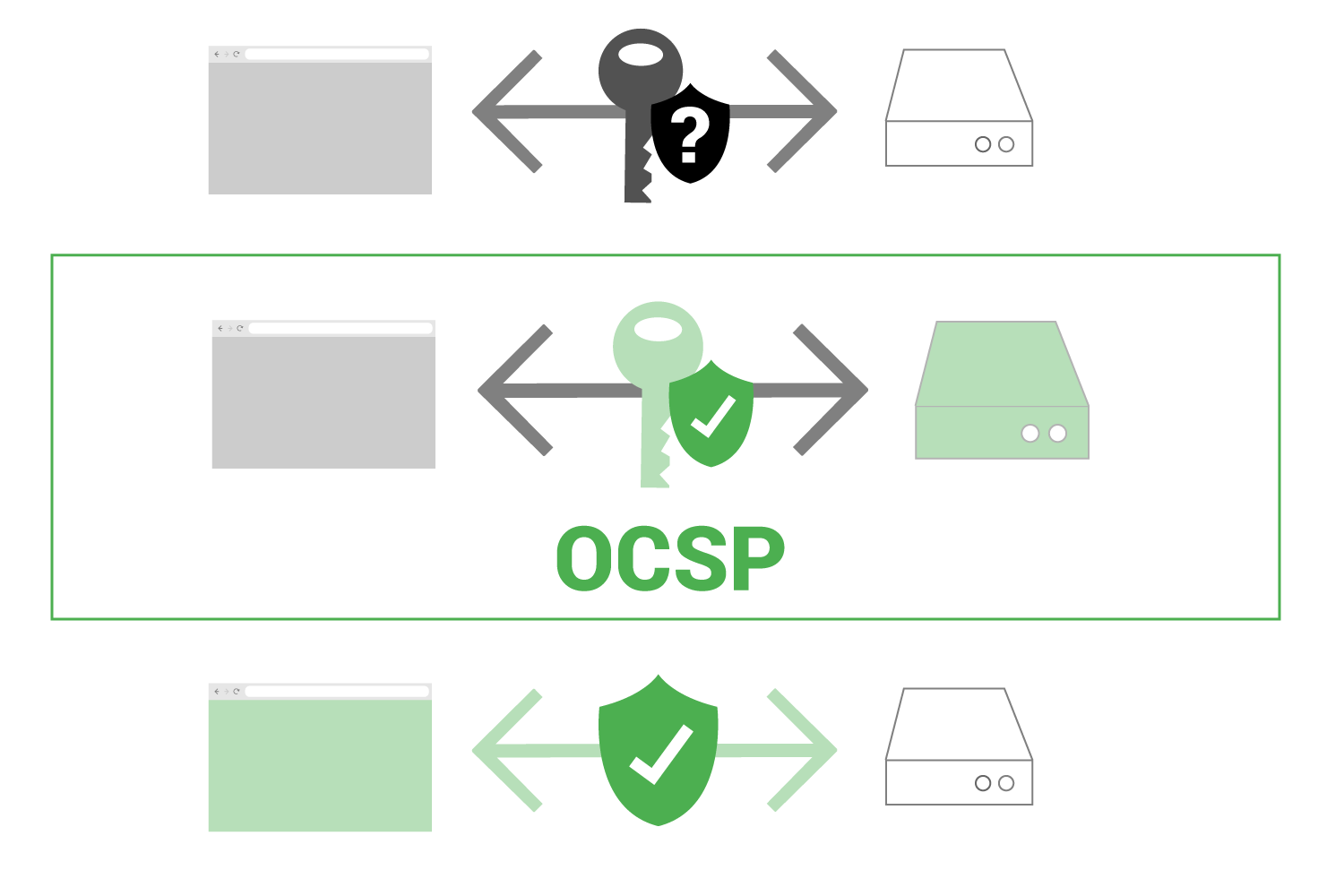
Using OCSP browsers verifies the validity of the SSL certificate to be sure it's non-revoked.
Realized using OCSP Stapling technology (OCSP stapling).
The web server downloads a copy of the authentication center response, which is sent to the browser.
The OCSP Stapling method helps you quickly and securely check the validity of an SSL certificate. Verification sequence of the validation using OCSP Stapling technology consists of the following steps:
Step 1. The web server hosting the SSL-protected website sends the request to the certifying center. In response from the CA, the status of the certificate comes along with a signed timestamp (timestamp). Signing a tag allows you to ensure that it will not be changed in any way by the webserver.
Step 2. The visitor's browser connects to the server. At this point, the server binds the timestamp received from the CA to the SSL certificate.
Step 3. Web browser checks the timestamp. It is signed by the certificate supplier, which means that it can be trusted.
Step 4. If the certificate is trusted, then the browser will open the page.
Otherwise, the user will receive an error message.
This approach allows you to remove the load from the certification centers and transfer it to web hosting. As a result, SSL connections are installed faster, which helps protect confidential information from users from getting into the hands of intruders.
OCSP Stapling achieves several goals:
- Guarantees the security and confidentiality of user data ;
- Users are more likely to download protected content because browsers do not need to make multiple requests ;
- The bandwidth on the client-side is preserved, which is an advantage for mobile users ;
- Increased confidence and customer satisfaction by increasing the speed of delivery of protected content ;
